Mastering the Walled Garden: The New Era of Sideloading on Android Gadgets
Introduction: The Crossroads of Security and Openness
For over a decade, the defining characteristic separating Android phones from their competitors has been the philosophy of openness. Unlike the rigid “walled garden” approach of iOS, Android has historically allowed users to install software from anywhere they choose—a process known as sideloading. This freedom has been the bedrock of the enthusiast community, allowing for the proliferation of open-source repositories like F-Droid, game emulators, and specialized tools that Google Play might deem too niche or controversial. However, the landscape of mobile security is shifting rapidly.
As mobile devices become the primary repository for our digital identities and financial lives, the vectors for attack have multiplied. In response, Google is orchestrating a significant paradigm shift in how the operating system handles external applications. Recent Android news indicates a move toward stricter default restrictions on sideloading to protect the average consumer from sophisticated phishing scams and malware. Yet, in a nod to its roots, the ecosystem is retaining a critical “escape hatch” for power users.
This article explores the nuances of these upcoming changes, detailing how Android gadgets will balance mass-market safety with enthusiast freedom. We will delve into the technical mechanisms of these restrictions, how the bypass systems function for developers and power users, and the best practices for navigating this new, more secure, yet complex environment.
Section 1: The Evolution of the “Unknown Source”
From Toggle to Permission: A History of Sideloading
To understand the future, we must look at the trajectory of Android’s security model. In the early days (Android 7 and below), sideloading was a global setting: a single toggle for “Allow installation from unknown sources.” Once flipped, the gate was open for any app to install another app. This was simple but dangerous.
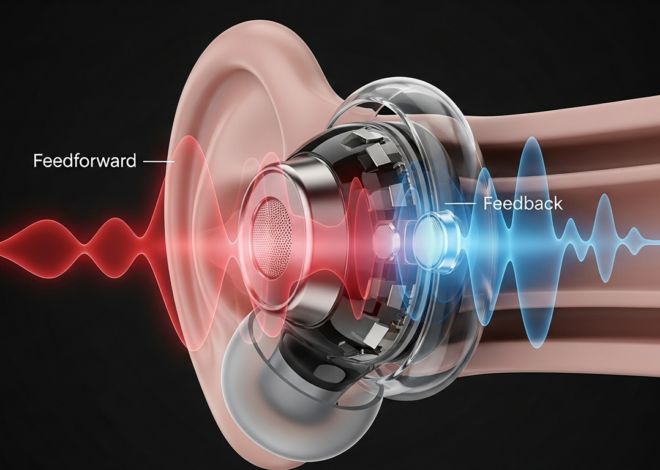
Modern Android phones evolved this into a per-app permission model. Today, if you want to install an APK file downloaded via Chrome, you must explicitly grant Chrome the permission to “Install unknown apps.” While this reduced accidental infections, social engineering attacks have become more sophisticated. Scammers now guide victims through these prompts over the phone, bypassing the operating system’s warnings through manipulation rather than technical exploits.
The Case for Stricter Defaults
The impetus for tightening these restrictions is not purely about control; it is largely about financial safety. Sideloading is the primary vector for banking trojans and accessibility abuse malware. By restricting the ability of standard users to easily install APKs from messaging apps or browsers, Google aims to cut off the supply chain for these attacks.
However, this creates a friction point for legitimate use cases. Many Android gadgets rely on sideloading for beta testing, enterprise app deployment, or accessing region-locked content. The challenge for the platform architects is to create a system that defaults to “Fort Knox” for the casual user while remaining a sandbox playground for the developer and the power user.
Section 2: Deep Dive into Restrictions and the Power User Bypass
The Mechanism of the New Restrictions
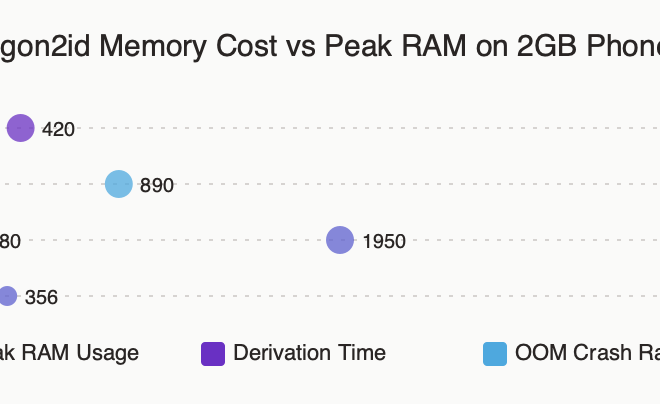
The upcoming changes to the Android operating system are expected to introduce a tiered approach to app installation. Rather than a simple warning, the system may block sideloading entirely by default under certain “Advanced Protection” configurations or for users enrolled in specific security programs. This goes beyond the standard Google Play Protect scanning.

The system likely leverages the Play Integrity API and stricter enforcement of the REQUEST_INSTALL_PACKAGES permission. When a user attempts to open an APK file, the Package Installer verifies the source. If the source is not a trusted app store and the device is in a standard security state, the installation could be halted with a message indicating that sideloading is currently disabled by the administrator or the OS vendor.
The “Power User” Escape Hatch
Crucially, the open nature of Android is being preserved through a deliberate bypass mechanism. This is not a loophole, but a feature designed for those who understand the risks. This bypass is expected to be housed within the Developer Options menu.
How the Bypass Works:
- Activation: Users will likely need to unlock Developer Options (typically done by tapping the “Build Number” in settings seven times).
- The Toggle: A specific setting, potentially labeled “Allow app installs from external sources” or a modification of “USB Debugging” privileges, will override the global block.
- ADB (Android Debug Bridge): For the ultimate power user, the ability to install apps via ADB commands (e.g.,
adb install package_name.apk) from a computer remains the gold standard. This method bypasses the on-device interface restrictions entirely, assuming the user has physical access and has authorized the debugging connection.
This bifurcation creates two distinct user experiences: a “console-like” secure experience for the general public, and a traditional “PC-like” open experience for enthusiasts who actively seek it out.
Section 3: Implications for the Ecosystem and Developers
Impact on Third-Party App Stores
The tightening of sideloading rules has profound implications for the alternative app store market. Stores like F-Droid, the Amazon Appstore, and manufacturer-specific stores (like the Samsung Galaxy Store) rely on the ability to update apps and install new ones.
If the new restrictions require users to dive into Developer Options to enable these stores, user acquisition for third-party marketplaces will face significant friction. However, recent regulatory pressures, such as the Digital Markets Act (DMA) in Europe, are forcing Google to make third-party stores easier to use. We are likely to see a split where “Authorized Alternative Stores” are whitelisted, while raw APK installations from the web face the new hurdles.
The Enterprise and Corporate Sector
For businesses deploying proprietary software to Android gadgets used in the field—such as logistics scanners or POS systems—these changes require updated Mobile Device Management (MDM) strategies. IT administrators will need to ensure that their deployment methods are whitelisted or that devices are provisioned in a way that bypasses consumer-grade restrictions without compromising corporate security.
The “Slippery Slope” of Walled Gardens
There is a philosophical debate within the Android news community regarding these changes. Critics argue that hiding sideloading capabilities behind Developer Options is the first step toward removing them entirely. They point to the gradual locking down of the /system partition and the complexities of rooting modern devices as evidence.

However, proponents argue that this separation is necessary for Android to mature. By segregating “unsafe” behaviors to a mode that requires technical knowledge to activate, Android can shed its reputation for malware susceptibility while technically remaining open source and modifiable.
Section 4: Best Practices for Sideloading in the New Era
For the power user intending to utilize the bypass mechanisms, security becomes a personal responsibility. Without the safety net of the default OS restrictions, users must adopt rigorous hygiene when managing their Android phones.
1. Verify Signature Checksums
When downloading an APK from a site like APKMirror or a GitHub repository, never blindly install it. Use a file manager that supports checksum verification. Compare the SHA-256 hash of the downloaded file with the hash provided by the developer. This ensures the file hasn’t been tampered with or injected with code during transit.
2. Utilize Sandboxing Applications
If you must run an app from a dubious source, consider using virtualization or sandboxing tools available on Android. Apps like “Shelter” or “Island” utilize Android’s Work Profile feature to isolate apps from your main personal data. If a sideloaded app is malicious, its access is limited to the sandbox, protecting your contacts, photos, and banking apps.
3. The Role of ADB App Control
For advanced management, learn to use ADB App Control tools on your PC. This allows you to install, disable, and manage permissions for sideloaded apps with greater granularity than the phone’s UI allows. It also serves as the primary method for utilizing the bypass if the on-device UI options become too restrictive.
4. Keep “Install Unknown Apps” Revoked
Even if you enable the power user bypass, follow the principle of least privilege. Do not leave the “Install unknown apps” permission enabled for your browser or file manager permanently. Grant it only when you are actively installing a specific app, and revoke it immediately after. This prevents “drive-by” downloads from executing without your notice.
Conclusion
The narrative surrounding Android gadgets is evolving from one of unrestricted chaos to one of structured freedom. The upcoming changes to sideloading represent a maturation of the platform, acknowledging that the average user needs protection from an increasingly hostile digital environment, while the enthusiast needs the tools to tinker and explore.
By moving unrestricted sideloading behind the “Power User” curtain of Developer Options, Google is attempting to have its cake and eat it too: providing an iOS-level safety net for the masses while preserving the Linux-based liberty that defines Android. For the informed user, the capability to control their device remains intact; it simply requires a more deliberate, conscious action to unlock. As we move forward, the definition of an “Android Power User” will increasingly be defined by those who know how to navigate these gates, taking ownership of both their device’s capabilities and its security.