Android’s New Security Frontier: A Deep Dive into Verified Sideloading
For years, the Android ecosystem has been defined by a core philosophical debate: the balance between user freedom and platform security. Unlike its more walled-off competitors, Android has long championed the ability for users to “sideload” applications—installing them from sources outside the official Google Play Store. This openness has been a hallmark for power users, developers, and enthusiasts, fostering a vibrant ecosystem of alternative app stores and independent software. However, this freedom has also been a double-edged sword, creating a primary vector for malware and security threats. Now, the landscape is set for a monumental shift. In a move poised to redefine platform security, Android is evolving its approach to sideloading, introducing a new paradigm of mandatory verification that will fundamentally change how we install apps on our beloved Android gadgets.
This article provides a comprehensive technical deep dive into this upcoming change. We will explore the evolution of app installation on Android, dissect the technical mechanisms behind the new verification process, analyze the profound implications for users and developers, and offer practical advice for navigating this new era. This isn’t just a minor update; it’s a foundational change to Android’s security architecture, and understanding it is crucial for everyone in the ecosystem.
The Evolution of App Installation on Android
To fully grasp the significance of the upcoming changes, it’s essential to understand the journey of app installation on Android. The platform’s approach has been one of gradual iteration, slowly adding layers of security while trying to preserve its open nature.
From a Single Switch to Granular Control
In the early days of Android, sideloading was controlled by a single, system-wide toggle: “Allow installation of apps from unknown sources.” Tucked away in the security settings, flipping this switch opened the floodgates, allowing any application to be installed from any source—a downloaded file, an email attachment, or a third-party app store. While empowering, this “all-or-nothing” approach was a significant security liability. A user might enable it for one legitimate app, forget to turn it off, and later become vulnerable to a malicious app installed without their explicit, moment-to-moment consent.
Recognizing this flaw, Google introduced a major change with Android 8.0 Oreo. The single global toggle was deprecated in favor of a more granular, per-app permission model. Under this system, users grant individual apps the ability to install other applications. For example, to install an APK downloaded via Chrome, you must first grant Chrome the “Install unknown apps” permission. This was a significant step forward, forcing a conscious user decision at the point of installation and preventing rogue apps from installing malware in the background. However, it still placed the ultimate responsibility—and the risk—squarely on the user’s shoulders.
The New Paradigm: Mandatory Real-Time Verification
The next evolutionary step moves beyond user-granted permission to system-enforced verification. The forthcoming model will require that nearly all applications, regardless of their installation source, undergo a mandatory, real-time security scan before the OS will allow them to be installed. This effectively extends the powerful protections of Google Play Protect to the entire device, not just apps sourced from the Play Store. It’s a fundamental shift from a policy of “install at your own risk” to “install only if verified safe.” This development is one of the most significant pieces of Android news in recent years, signaling a clear prioritization of security for the platform’s billion-plus users.
A Technical Breakdown of the Verification Process

The new system is more than just a simple warning; it’s a sophisticated, multi-layered security check integrated at the OS level. Understanding its mechanics reveals the depth of this change and how it aims to neutralize threats before they can ever execute on a user’s device.
How the Verification Will Likely Work
When a user attempts to install an APK file from any source outside the Play Store, the Android Package Manager service will intercept the request. Before proceeding with the installation, it will initiate a verification sequence. This process will likely involve several steps:
- Metadata and Signature Analysis: The system will first inspect the app’s digital signature and package metadata. It will send a hash of the APK and its signing certificate to Google’s backend servers.
- Backend Cross-Referencing: Google’s servers will check this information against a massive, constantly updated database of known malware, spyware, and potentially harmful applications (PHAs). This is an extension of the same technology that powers Google Play Protect.
- Heuristic and Static Analysis: If the app is not on a known blacklist, the system may perform a lightweight static analysis, scanning the app’s code for suspicious patterns, dangerous API calls, or attempts to exploit known vulnerabilities without running the code itself.
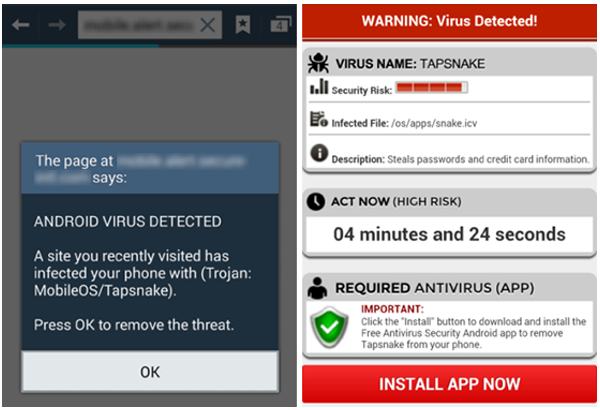
- Verdict and Enforcement: The server returns a verdict to the device. If the app is deemed safe or is unknown but shows no malicious indicators, the installation is allowed to proceed. If it is identified as a known threat or exhibits highly suspicious characteristics, the OS will block the installation entirely, presenting the user with a non-dismissible warning explaining the risk.
Defining an “Unverified” or Malicious App
The criteria for an app failing this verification check will be stringent. An app is likely to be blocked if it meets one or more of the following conditions:
- Known Malware Signature: The app’s package hash or developer signature matches a known malicious entity in Google’s security database.
- Deceptive Behavior: The app attempts to impersonate a legitimate application (e.g., using the icon and name of a banking app) or uses obfuscation techniques commonly associated with malware.
- Exploitation of Privileges: The app requests an excessive number of permissions that don’t align with its stated purpose or contains code designed to exploit system vulnerabilities to gain elevated access.
- Violation of Core Policies: Even if not strictly malware, an app that facilitates illegal activities or violates fundamental developer policies (like those against hate speech or egregious data collection) could be blocked.
This robust, cloud-powered check transforms the security of Android phones from a reactive model (scanning apps after installation) to a proactive one (preventing installation in the first place).
Implications for the Android Ecosystem
This fundamental change will send ripples across the entire Android ecosystem, affecting everyone from the average user to independent developers and alternative app marketplaces. The trade-offs between security and openness are at the forefront of this evolution.
What This Means for End-Users
For the vast majority of Android users, this change is an unambiguous security victory. It provides a powerful safety net that protects against accidental malware installation, a common issue for less tech-savvy individuals who might be tricked by social engineering. The peace of mind knowing that any app, from any source, has been vetted by Google’s security infrastructure is a massive enhancement to the platform.
However, for power users and enthusiasts, this raises questions about user autonomy. What happens if a legitimate, but niche, application is incorrectly flagged as a false positive? Consider a powerful system utility or a modded version of an open-source app that requires deep system access. These could potentially be blocked by a verification system tuned to be risk-averse. The key question will be whether Google provides a sufficiently accessible, albeit heavily firewalled, override mechanism for developers and true power users who understand and accept the risks.
Real-World Scenario: A user wants to install a custom version of a video player from a developer’s forum that includes a non-standard codec. Previously, they would simply enable installation for their browser and install the APK. Under the new system, if the app’s custom code is flagged by the heuristic analysis as “unusual,” the OS might block the installation, leaving the user without recourse unless a developer override is available and enabled.
The Impact on Developers and Alternative App Stores
This new verification mandate will require significant adjustments from developers who distribute their apps outside of Google Play. Independent developers who host APKs on their websites for beta testing or direct sales must now ensure their apps are built to pass these stringent checks. This may involve a new, lightweight registration process with Google to establish a trusted developer identity, even for off-Play-Store distribution.
The impact on alternative app stores like F-Droid (a repository for free and open-source software) or the Amazon Appstore could be substantial. These platforms will need to ensure their entire catalog can pass Google’s verification. For a platform like F-Droid, which builds apps from source code to ensure transparency and security, this introduces a new dependency on Google’s centralized verification system. It could create friction if their build process or the nature of certain open-source apps conflict with Google’s verification criteria.
Navigating the New Landscape: Recommendations and Considerations
Adapting to this new reality requires a proactive approach from all parties. The transition will be smoother for those who understand the changes and prepare accordingly.
Best Practices for Users

- Trust the System: For over 99% of use cases, this new verification layer is a benefit. Don’t seek out complex workarounds unless you are an advanced user who fully understands the security implications.
- Understand the Overrides (If Available): If Google implements a developer-level override, treat it with extreme caution. Enabling it should be a deliberate, temporary action for a specific, trusted purpose, not a permanent setting.
- Continue to Use Trusted Sources: While the system provides a safety net, it’s not infallible. The best practice remains to download apps from reputable sources like the Google Play Store or established, trusted alternative markets.
Key Considerations for Developers
- Maintain Good App Hygiene: Ensure your app only requests the permissions it absolutely needs. Avoid using obfuscation techniques that could be misconstrued as malicious by automated scanners.
- Properly Sign Your Applications: Using a consistent, secure, and verifiable digital signature will be more critical than ever to establishing your app’s identity and trustworthiness.
- Stay Informed: Closely follow announcements on the Android Developers Blog and documentation for official guidelines on the verification process. Early adoption of best practices will prevent your app from being blocked upon the system’s rollout.
Pros vs. Cons at a Glance
Pros:
- Dramatically enhanced security for the entire user base.
- Significant reduction in the spread of malware and PHAs.
- Creates a safer, more trustworthy ecosystem for all Android gadgets.
- Protects vulnerable users from social engineering attacks.
Cons:
- A reduction in absolute user freedom and control.
- Potential for false positives to block legitimate niche or developer-focused apps.
- Increased centralization of app distribution control under Google.
- Potential new hurdles for independent developers and alternative app stores.
Conclusion: A More Mature, More Secure Android
The introduction of mandatory real-time verification for sideloaded apps marks a pivotal moment in Android’s history. It represents a deliberate and decisive move to address the platform’s single greatest security challenge, bringing a new level of protection to millions of users. This change signals the maturation of the Android platform, evolving from its “wild west” origins into a more secure and stable ecosystem. While this shift inevitably involves a trade-off with the absolute openness that once defined it, the immense security benefit for the average user is undeniable. The future of Android phones is one where freedom and security are not opposing forces, but rather carefully balanced elements in a sophisticated, modern operating system.