Beyond the Browser: A Deep Dive into the Multi-Layered Security of Modern Android Phones
Fortifying Your Digital Fortress: Understanding Android’s Complex Security Landscape
In our hyper-connected world, the smartphone has become the epicenter of our digital lives. It’s our communication hub, wallet, photo album, and primary gateway to the internet. This centralization of data makes modern Android phones a high-value target for malicious actors. Headlines frequently flash with news of vulnerabilities, from sophisticated operating system exploits to widespread browser flaws that seem to put billions of devices at risk. While these alerts are crucial, they often paint an incomplete picture, focusing on a single point of failure without exploring the robust, multi-layered defense systems designed to protect you.
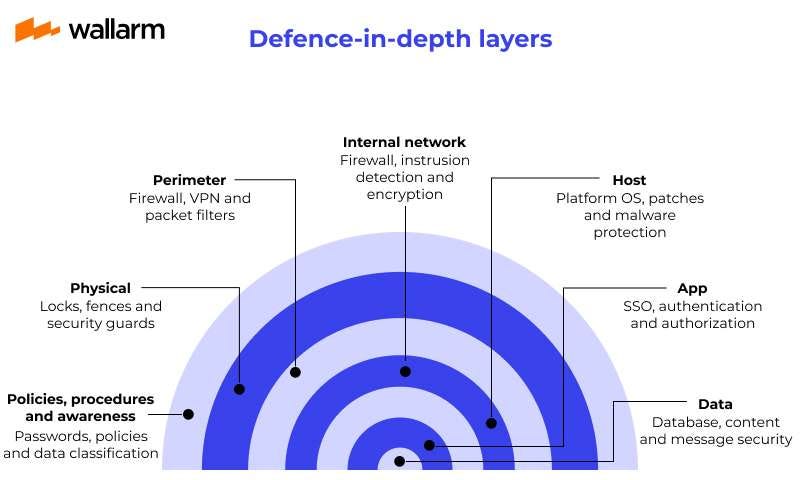
True digital security isn’t about a single, impenetrable wall; it’s about defense-in-depth. Android’s security model is a prime example of this philosophy, architected as a series of concentric rings of protection. From the low-level Linux kernel to the application sandbox and user-facing controls, each layer is designed to contain and mitigate threats. Understanding this architecture is no longer just for developers or security researchers; it’s essential knowledge for any user who wants to move from being a passive victim to an empowered guardian of their own data. This article will take you beyond the headlines and into the technical core of Android security, exploring its strengths, its inherent challenges, and the practical steps you can take to harden your most personal device.
Section 1: The Android Security Architecture: A Fortress of Layers
At its core, Android is built upon a security philosophy of privilege separation and isolation. The system assumes that no application is trustworthy by default and erects strong barriers to prevent a single compromised app from jeopardizing the entire system. This is achieved through several fundamental architectural layers.
The Linux Kernel Foundation
Android’s security story begins with its foundation: the Linux kernel. This isn’t just a convenient open-source choice; it’s a strategic one. The Linux kernel provides a battle-tested foundation for a multi-user operating system, which Android leverages to create its application sandbox. Key features inherited from Linux include:
- User-Based Permissions: Each Android application is assigned a unique User ID (UID) at installation. The kernel enforces security at the process level, ensuring that an application can only access its own files and resources. It’s like giving every app its own locked room, and only the kernel holds the master key.
- Process Isolation: The kernel ensures that the memory space of one application is completely segregated from another. An app cannot read or write to the memory of another process, which is a fundamental defense against data theft and interference between apps.
- Secure Inter-Process Communication (IPC): When apps do need to communicate (e.g., sharing a photo from your gallery to a social media app), they must use explicit, kernel-managed IPC mechanisms like Binders, which are governed by strict permission checks.
The Application Sandbox
Building on the kernel’s foundation, the Android Application Sandbox is arguably the most critical security feature for users. The sandbox ensures that every application, whether it’s your banking app or a simple game, runs in a restricted environment. When you install an app, the system creates a private directory for it that no other app can access by default. If a malicious app manages to get installed on your device, the sandbox severely limits the damage it can do. It cannot, for instance, read your emails from the Gmail app, steal your chat logs from WhatsApp, or access photos stored by your camera app without being explicitly granted permission by you, the user, through a system-managed prompt.
System-Level Protections and Verified Boot

Beyond sandboxing, Android employs numerous system-level protections. Address Space Layout Randomization (ASLR) makes it harder for attackers to predict memory locations to execute malicious code. Verified Boot creates a chain of trust from the hardware level up to the operating system, ensuring that the software running on your device hasn’t been tampered with. When you power on your phone, the bootloader checks the signature of the operating system. If it detects a modification or corruption (potentially from malware), it will warn you or refuse to boot, preventing a compromised OS from running. This is a critical defense against persistent threats that try to embed themselves deep within the system.
Section 2: The Browser: Your Primary Gateway and Greatest Vulnerability
While the OS provides a strong fortress, every fortress has a main gate. On modern Android gadgets, that gate is the web browser. It’s the application we use to explore the untrusted wilds of the internet, making it the most exposed and frequently targeted component of your phone.
Why Browsers Are a Prime Target
Web browsers are enormously complex pieces of software. They have to parse and execute code (HTML, CSS, JavaScript) from untrusted sources, manage sensitive data like cookies and passwords, and interact with device hardware like your camera and microphone. This complexity creates a massive attack surface. A single vulnerability in the browser’s rendering engine or JavaScript interpreter can potentially lead to a “drive-by download” where malware is installed simply by visiting a malicious webpage, or a “zero-click” exploit that requires no user interaction at all. Because browsers are the conduit for so much of our online activity, a compromise here can be devastating, potentially exposing login credentials, financial information, and personal communications.
The Chromium Engine: A Blessing and a Curse
The vast majority of browsers on Android—including Google Chrome, Samsung Internet, Microsoft Edge, and Brave—are built on the open-source Chromium project. This has benefits, as security researchers and Google’s own Project Zero team constantly audit Chromium’s code, finding and fixing flaws. However, it also creates a monoculture. A critical vulnerability discovered in the core Chromium engine, such as in its V8 JavaScript engine or Skia graphics library, instantly affects billions of users across hundreds of different browsers and platforms. This is why you’ll often see urgent “update your browser now” alerts in **Android news**; a single flaw can have a truly global impact, making a rapid, coordinated patch rollout absolutely essential.
Android’s Containment Strategy
Even if your browser is compromised, Android’s defense-in-depth model kicks in. The browser, like any other app, runs within its own application sandbox. Therefore, an exploit that achieves code execution *within the browser’s process* is still contained. The malicious code cannot automatically read files from your other apps or access your hardware without a second exploit that breaks out of the sandbox. This containment is a crucial fallback, turning a potentially catastrophic system-wide compromise into a more limited, application-specific one. It highlights why OS-level security is just as important as application-level security.
Section 3: The Ecosystem’s Double-Edged Sword: Fragmentation and Updates
Android’s greatest strength—its open nature and diverse ecosystem of hardware manufacturers—is also its most significant security challenge. Unlike Apple, which controls both the hardware and software for iOS, Google provides the base Android OS to dozens of manufacturers who then modify it for their specific devices. This leads to a phenomenon known as fragmentation.

The Fragmentation and Update Latency Challenge
When Google discovers and patches a security vulnerability, it releases the fix in its monthly Android Security Bulletin. However, that’s only the first step. The patch must then be picked up by chip manufacturers (like Qualcomm or MediaTek), then by the device manufacturer (like Samsung, OnePlus, or Motorola), who integrate it into their custom versions of Android. Finally, in some regions, cellular carriers must approve the update before it’s pushed to your phone. This multi-stage process can introduce significant delays, sometimes lasting weeks or even months. During this “patch gap,” users remain vulnerable to known exploits. This is a common pitfall for many Android phones, especially budget models or older devices that no longer receive timely support.
A real-world case study that perfectly illustrates this is the “Stagefright” vulnerability from 2015. This critical flaw in Android’s media playback engine could allow an attacker to execute code by simply sending a specially crafted MMS message. The user didn’t even have to open the message. The vulnerability affected nearly a billion devices, and the fragmented nature of the ecosystem made patching a slow, arduous process, leaving millions of users exposed for an extended period. The public outcry from Stagefright was a major catalyst for change, pushing Google and manufacturers to streamline the update process.
Google’s Solutions: Project Mainline and Security Patch Levels
To combat fragmentation, Google has introduced several major initiatives. Project Treble (introduced in Android 8.0) modularized the OS, separating the core Android framework from manufacturer-specific code to speed up updates. More recently, Project Mainline (introduced in Android 10) takes this a step further. It allows Google to update critical OS components directly through the Google Play Store, bypassing the manufacturer and carrier entirely. This means core security components, like media frameworks and DNS resolvers, can be patched as quickly and easily as updating an app.
For users, the most visible result of these efforts is the “Android security patch level” found in your phone’s settings (usually under “About phone”). This date tells you how up-to-date your device is with Google’s security fixes. A device with a patch level from three months ago is missing three months’ worth of publicly known security fixes, making it a much easier target for attackers.
Section 4: Best Practices for Hardening Your Android Device
While Google and device manufacturers provide the security foundation, the user plays the final and most critical role in the security chain. Your habits and awareness can significantly enhance the built-in protections of your Android phone.
Actionable Tips and Recommendations
Here are concrete steps every user should take to secure their device:
- Update Diligently: This is the single most important action you can take. Enable automatic updates for both the operating system and your applications. When you see a notification for a system update, don’t ignore it. That update contains crucial security fixes. Pay special attention to browser updates, as they are on the front line of defense.
- Scrutinize App Permissions: Modern Android gives you granular control over what apps can access. When an app asks for permission to your contacts, location, or microphone, ask yourself: does it truly need this for its core function? A simple calculator app has no business accessing your contacts. Regularly audit your app permissions in Settings and revoke any that seem unnecessary.
- Source Apps from the Google Play Store: While it’s possible to “sideload” apps by installing APK files from the web, this is extremely risky. The Google Play Store, while not perfect, benefits from Google Play Protect, which scans billions of apps daily for malware. Sticking to the official store dramatically reduces your risk of installing a malicious application.
- Enable Enhanced Safe Browsing in Chrome: Within your Chrome settings, you can enable “Enhanced Safe Browsing.” This feature provides more proactive, real-time protection against phishing, malware, and dangerous websites by sending more data to Google for analysis.
- Secure Your Google Account: Your Google account is the key to your digital kingdom. Protect it with a strong, unique password and, most importantly, enable Two-Factor Authentication (2FA). With 2FA enabled, even if an attacker steals your password, they cannot access your account without the second factor (a code from your phone or a physical security key).
- Be Wary of Public Wi-Fi: Unsecured public Wi-Fi networks are a breeding ground for “man-in-the-middle” attacks. Avoid logging into sensitive accounts (like banking) on public networks. If you must use them frequently, invest in a reputable Virtual Private Network (VPN) service to encrypt your traffic.
Conclusion: A Shared Responsibility
The security of your Android phone is a dynamic and layered partnership. Google builds a robust and secure foundation with the Linux kernel and the application sandbox, constantly working to mitigate fragmentation with initiatives like Project Mainline. Device manufacturers are responsible for implementing these protections and delivering timely updates. But ultimately, you, the user, are the final gatekeeper. Your choices—the apps you install, the permissions you grant, the links you click, and the diligence with which you update your software—form the outermost and most adaptable layer of defense.
By understanding the architecture beneath the surface, you can better appreciate the importance of security updates and make more informed decisions. The threats will continue to evolve, but a combination of Android’s powerful built-in protections and your own vigilant, proactive habits can create a formidable defense, ensuring your digital fortress remains secure in an ever-changing landscape.