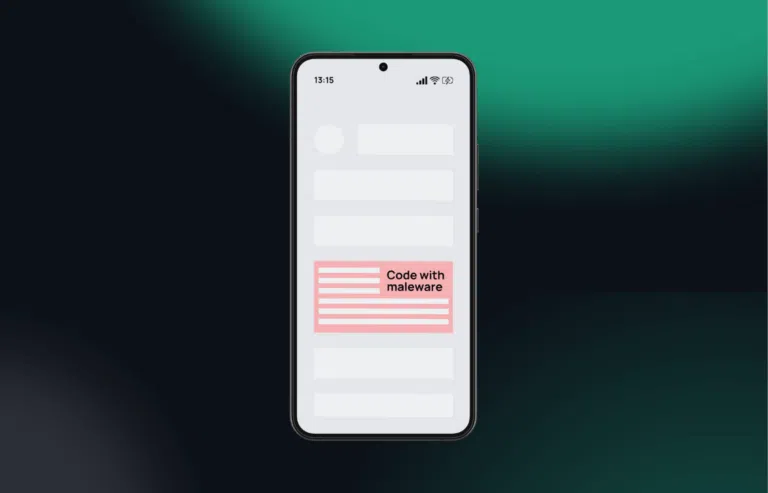
Ghost in the Machine: How New Android Malware Fakes Human Behavior to Evade Detection
The Evolving Threat Landscape of Android Security
The world of mobile security is a relentless battlefield, a constant arms race between cybercriminals and security professionals. For years, malware detection on Android devices has relied on a combination of signature-based scanning and behavioral heuristics. Security systems have become adept at spotting the tell-tale signs of a malicious bot: impossibly fast data entry, rigid command-and-control communication, and automated actions that no human could perform. However, the latest Android News from the security frontlines reveals a disturbing and sophisticated evolution in malware design. A new generation of threats is emerging, engineered not just to steal data, but to do so with the subtlety and patience of a human user.
This new class of malware meticulously mimics human interaction—simulating keystrokes with realistic delays, navigating menus with deliberate pauses, and tapping buttons with non-uniform timing. By cloaking its malicious activities in the guise of legitimate user behavior, it aims to become a ghost in the machine, slipping past the very behavioral analysis systems designed to catch it. This article provides a comprehensive technical deep dive into this emerging threat, exploring its mechanisms, the profound implications for the entire Android ecosystem, and the critical defense strategies that users and developers must adopt to stay ahead in this escalating conflict.
The Anatomy of a New Evasive Threat: Beyond Traditional Malware
To understand the gravity of this new threat, we must first look beyond the traditional “smash and grab” tactics of older malware. While the end goal remains the same—exfiltrating sensitive data like banking credentials, personal messages, and contact lists—the methodology has undergone a radical transformation. This new approach is built on a foundation of stealth and deception, prioritizing long-term persistence over short-term gains.
What is Behavior-Mimicking Malware?
Behavior-mimicking malware represents a significant leap in evasion techniques. Its core principle is to bypass security solutions that flag non-human, or bot-like, activity. Modern security platforms, including Google Play Protect and third-party antivirus applications, employ sophisticated heuristics to analyze how applications interact with the operating system and other apps. If an application fills out a login form and password field in 15 milliseconds, it’s an obvious red flag for automation. This new malware circumvents this by executing its commands with a “human” touch.
Instead of instantly pasting stolen credentials into a banking app, the malware will programmatically “type” them out, character by character. It introduces randomized delays between each keystroke, mimicking the natural cadence of a person typing on a touchscreen. This seemingly simple trick is devastatingly effective at fooling systems designed to differentiate between human and machine input, allowing the malware to operate undetected for longer periods.
Key Characteristics and Capabilities
While the human mimicry is its most novel feature, this malware is typically built upon a suite of well-established malicious capabilities that work in concert to compromise a user’s device.

- Accessibility Services Abuse: The primary infection vector often involves social engineering a user into granting powerful Accessibility Services permissions. Designed for users with disabilities, this service allows an app to read the screen content and perform actions on the user’s behalf. Once granted, the malware has the keys to the kingdom, enabling it to perform overlay attacks, capture keystrokes, and grant itself further permissions without user interaction.
- Advanced Overlay Attacks: The malware can detect when a user opens a sensitive application, such as a banking or social media app. It then places a perfectly crafted, invisible overlay on top of the legitimate app’s login screen. When the user enters their username and password, they are actually typing into the malware’s fake window, which captures the credentials before passing them to the real app to avoid suspicion.
- Data Exfiltration: Armed with extensive permissions, the malware can scrape virtually any data from infected Android Phones. This includes SMS messages (often to intercept two-factor authentication codes), contact lists, call logs, and files stored on the device. All this stolen information is then quietly sent to a remote command-and-control (C2) server.
A Technical Deep Dive: How Malware Fakes Being Human
The true innovation of this malware lies in its ability to exploit the assumptions baked into modern security software. By understanding how behavioral analysis works, its creators have engineered a way to subvert it from within. This requires a nuanced understanding of both Android’s architecture and the principles of cybersecurity heuristics.
Exploiting the Flaw in Behavioral Heuristics
Behavioral heuristic analysis is a cornerstone of modern endpoint security. It operates on the premise that malicious software behaves differently from legitimate applications used by humans. It looks for patterns and anomalies, such as:
- Speed of Execution: Actions performed at machine speed, far faster than any human could manage.
- Input Method: Data being programmatically injected into fields rather than being typed.
- Interaction Patterns: Rigid, repetitive, and perfectly consistent navigation through an app’s UI.
Behavior-mimicking malware directly targets these assumptions. The code is specifically written to introduce imperfections and delays that make its actions appear organic. For security software, the malware’s activity log looks less like a script and more like a genuine user session, making it significantly harder to flag as malicious.
Mimicking Keystrokes and Taps
The core of the human simulation is the function that handles text input. Instead of using a simple `setText()` command to instantly populate a field, the malware iterates through a string of characters, injecting them one by one into the target input field. A simplified pseudo-code representation of this logic might look like this:
function simulateHumanTyping(targetUiElement, textToInput) {
// Convert the string into an array of characters
const characters = textToInput.split('');
for (const char of characters) {
// Generate a random delay to simulate human typing speed
// e.g., a value between 80ms and 250ms
const randomDelay = Math.floor(Math.random() * (250 - 80 + 1)) + 80;
// Pause execution for the generated delay
sleep(randomDelay);
// Append the next character to the UI element
targetUiElement.append(char);
}
}
This same principle is applied to UI navigation. Instead of instantly jumping between screens, the malware will simulate a “tap” on a button, wait for a variable period, and then proceed, mimicking the cognitive delay of a human user deciding their next action. This makes its entire operational lifecycle—from opening an app to transferring funds—appear deceptively legitimate.
Implications for the Android Ecosystem: A Shifting Battlefield
The emergence of malware that can convincingly fake human behavior has profound and far-reaching implications for everyone involved in the Android ecosystem, from the average user to the security researchers on the front lines.
For the Everyday User of Android Phones

For years, users have been informally trained to look for signs of infection, such as their device suddenly slowing down, apps crashing, or unusual battery drain. Behavior-mimicking malware is designed to be resource-efficient and stealthy, meaning these classic indicators may no longer appear. The line between a human and a bot operating on one’s device is becoming dangerously blurred. This increases the risk to personal and financial data stored on all kinds of Android Gadgets, from smartphones to tablets.
Consider a real-world scenario: A user’s banking credentials are stolen via a phishing attack. The malware, now active on their phone, waits for a low-activity period, like the middle of the night. It then opens the banking app, carefully “types” in the username and password, navigates to the transfer funds screen with human-like pauses, enters the details for a fraudulent transaction, and completes the transfer. The bank’s fraud detection system, which is trained to spot rapid, automated login and transfer sequences, might completely miss this slow, deliberate, and seemingly human-initiated activity.
For Security Researchers and Antivirus Vendors
This new evasion technique marks a significant challenge for the security industry. Signature-based detection, which relies on identifying known malware files, remains important but is clearly insufficient against polymorphic or novel threats. Even first-generation behavioral analysis is now being rendered less effective. The fight is moving to a more abstract level. Security tools must evolve to analyze not just the “what” (the action) but the “why” (the context). This requires more advanced machine learning models capable of discerning the subtle, contextual differences between a legitimate user session and a highly sophisticated malicious bot that is trying to act like one. This will necessitate training AI on massive datasets to better understand the nuances of true human interaction versus faked human interaction.
For Android App Developers
Developers, particularly those of financial, healthcare, and communication apps, can no longer afford to be passive about security. They must operate under the assumption that the underlying OS could be compromised. This means building more defenses directly into their applications. Techniques like detecting when an Accessibility Service is reading their app’s fields, checking for screen overlays, and implementing device attestation to verify the integrity of the operating environment are becoming essential, not optional, security features.
Protecting Your Digital Life: Actionable Defense Strategies
While this new malware is sophisticated, it is not invincible. A multi-layered defense strategy, combining user vigilance with robust security practices, remains the most effective way to protect your devices and data.
For Users of Android Phones and Gadgets
- Scrutinize All Permission Requests: Be extremely wary of any app that requests Accessibility Services permissions. Unless the app is a well-known tool for users with disabilities (like a screen reader), this request is a major red flag. Understand that granting this permission gives an app almost complete control over your device.
- Download Apps from Trusted Sources: The overwhelming majority of Android malware is distributed outside the Google Play Store. Stick to official app stores and avoid sideloading applications (installing from .APK files) from unverified websites or links.
- Keep Everything Updated: Regularly install updates for the Android operating system and all your applications. These updates frequently contain critical security patches that close the vulnerabilities exploited by malware.
- Enable Google Play Protect: Ensure this built-in security feature is active on your device. It scans your apps for malicious behavior and can warn you of potential threats.
- Consider a Reputable Mobile Security App: For an additional layer of protection, a high-quality mobile antivirus solution from a trusted vendor can help detect and block emerging threats that might slip past built-in defenses.
Best Practices for Developers
- Implement Stronger In-App Security: Don’t rely solely on the OS for security. Use tools to detect rooting, emulator environments, and the presence of screen overlays. The latest Android News on security often provides insights into new libraries and techniques for this.
- Secure Data Handling: Follow secure coding practices to ensure that sensitive data like API keys and user credentials are never stored in plaintext within your application’s code or local storage.
- Target Modern Android APIs: By targeting recent Android API levels, you can take advantage of the latest platform security features, including more granular permissions and restrictions on background processes.
Conclusion: The Ongoing Arms Race in Mobile Security
The emergence of malware that can convincingly mimic human behavior is a sobering reminder that the cybersecurity landscape is in a state of constant flux. This development represents not just an incremental improvement in malware design, but a strategic shift intended to undermine a core pillar of modern security: behavioral analysis. It proves that as our defenses become more intelligent, so too will the attacks designed to circumvent them.
For users of Android Phones, this underscores the timeless importance of digital hygiene and critical thinking. For developers and security professionals, it is a call to action to innovate and build more resilient, context-aware security systems. The arms race between attackers and defenders will continue, and staying protected requires a commitment to vigilance, education, and the continuous adoption of proactive security measures across the entire Android ecosystem.