The Future of Sideloading: Balancing Security and Power User Freedom on Android Gadgets
The Android operating system has long been defined by a philosophy of openness and user choice. Unlike its primary competitor, iOS, which has historically maintained a strict “walled garden” approach, Android Phones and tablets have allowed users to install software from virtually any source. This process, known as sideloading, is a cornerstone of the platform’s appeal to enthusiasts, developers, and power users. It allows for the installation of open-source repositories, legacy applications, and specialized tools that may not adhere to the strict policies of the Google Play Store.
However, the landscape of mobile security is shifting rapidly. As mobile devices become the primary repository for sensitive banking data, personal identification, and health metrics, the vectors for malware attacks have multiplied. In response, recent Android News suggests a significant paradigm shift in how the operating system handles external application installation. The challenge facing the platform’s architects is substantial: how to implement robust, enterprise-grade security measures to protect the average consumer without alienating the core demographic of power users who demand total control over their hardware.
We are entering a new era for Android Gadgets where the “Unknown Sources” toggle is no longer a simple binary switch. Instead, we are moving toward a sophisticated, tiered security model. This model aims to restrict accidental or malicious sideloading while preserving a bypass mechanism for those who truly understand the risks. This article delves deep into the technical nuances of these upcoming changes, the implications for the ecosystem, and how power users can navigate the future of Android security.
The Evolution of App Installation and Security Protocols
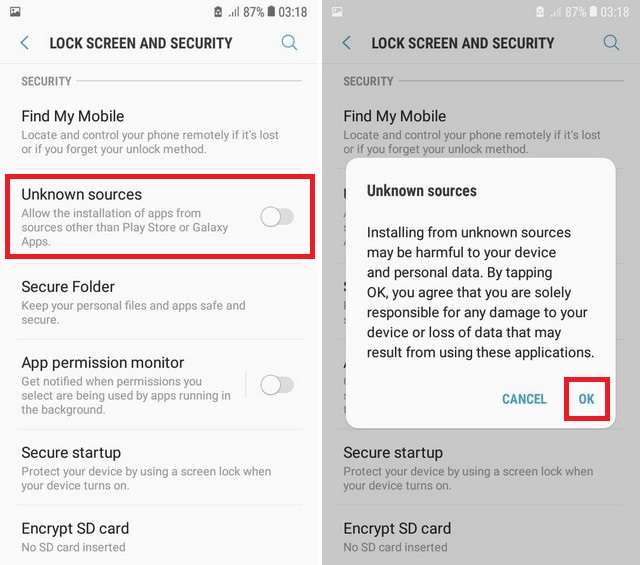
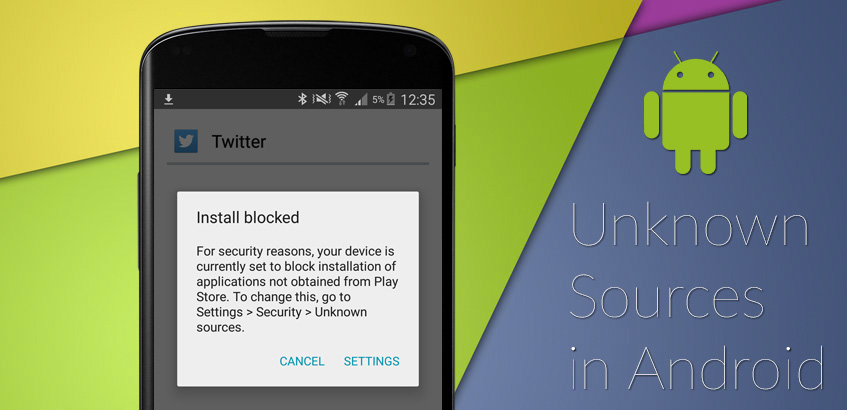
To understand the significance of new sideloading restrictions, one must first understand the history of package management on Android. Since the inception of the OS, the Android Package Kit (APK) has been the standard file format for distributing and installing mobile apps. For over a decade, enabling the installation of APKs from outside the Play Store required a user to navigate to settings and check a box allowing installation from “Unknown Sources.”
From Global Toggles to Per-App Permissions
In earlier versions of Android, this was a global setting. Once enabled, any app could download and install another app. This presented a massive security flaw; a seemingly innocent flashlight app could silently download a banking trojan. Google addressed this in later versions (Android 8.0 Oreo and beyond) by changing the permission model to “Install Unknown Apps” on a per-app basis. For example, a user has to explicitly grant the Chrome browser or a File Manager permission to trigger an installation package.
While this reduced drive-by downloads, it did not solve the issue of social engineering. Attackers simply tricked users into granting these permissions. Consequently, the narrative in recent Android News has focused on the integration of Google Play Protect—a built-in malware scanner—directly into the installation flow. The system now actively scans sideloaded APKs for malicious code signatures before allowing the installation to proceed.
The Rise of Heuristic Blocking
The latest developments in Android security go beyond simple signature matching. Modern Android Phones utilize heuristic analysis and machine learning to identify potentially harmful behavior, even in apps that haven’t been flagged before. This includes analyzing permissions requested by the APK (such as Accessibility Services or SMS reading capabilities) that are frequently abused by financial malware.
The new wave of restrictions is designed to intercept these installations at the system level. If an app utilizes sensitive APIs or outdated target SDK versions that bypass modern security sandboxes, the OS is increasingly likely to block the installation entirely. This moves the security posture from “warn the user” to “stop the user,” a controversial but arguably necessary step for mass-market safety.
Detailed Analysis: The Power User Bypass Mechanism
The critical distinction between Android and a fully closed ecosystem lies in the existence of an “escape hatch.” While the default behavior of Android Gadgets is becoming more restrictive, the commitment to power users remains through specific bypass mechanisms. Understanding how these mechanisms work is essential for developers and enthusiasts.
The “Restricted Setting” Logic
When the operating system identifies a sideloaded app as high-risk—perhaps because it requests access to notification listeners or accessibility services without a proven track record—it places the app in a “restricted setting” state. For the average user, the installation might appear to fail, or the app will install but be unable to access those specific permissions. The user interface will gray out the ability to grant these sensitive rights, protecting the user from social engineering attacks where a scammer instructs a victim to “click allow on everything.”
However, for power users, the system includes a deliberate workaround. This usually involves a multi-step process that confirms the user’s intent and technical literacy. This might involve navigating to the specific app info page within the system settings, accessing a hidden menu via the “three-dot” interface, and explicitly selecting “Allow Restricted Settings.” This creates a friction point that stops a grandmother from being scammed but allows a developer to test their automation tool.
Technical Implementation of the Bypass
The bypass mechanism is not merely a UI hurdle; it is a shift in how the `PackageManager` service validates installations. When a power user executes a bypass:
- Identity Verification: The system may require biometric authentication (fingerprint or face unlock) or the device PIN to confirm that the person authorizing the installation is the device owner, not a remote attacker.
- Logging and Telemetry: The OS likely logs this event as a “high-risk user action.” This data helps Google’s security algorithms understand that this specific device is managed by a user who accepts higher liability.
- Sandboxing Adjustments: Even with the bypass, the app may run in a stricter sandbox than a Play Store app, ensuring that if it does contain malicious code, its ability to laterally move to other parts of the system is contained.
Real-World Scenario: The F-Droid User
Consider a user attempting to install a specialized network monitor from F-Droid, an open-source app repository. This app requires root-level access or ADB (Android Debug Bridge) permissions to function. Under the new security regime, Play Protect might flag this app because it uses non-standard APIs.
A standard user would see a “Blocked by Play Protect” screen. A power user, however, understands that this is a false positive based on the app’s capabilities rather than its intent. By utilizing the bypass mechanism—likely found within the “More Details” section of the warning or through Developer Options—the power user can force the installation. This duality preserves the open nature of Android Phones while maintaining a safety net for the 99% of users who do not need network monitoring tools.
Implications for the Android Ecosystem
The tightening of sideloading restrictions, paired with a dedicated power user bypass, has profound implications for the broader ecosystem of Android Gadgets. This shift affects everyone from independent developers to enterprise IT managers.
Impact on Third-Party App Stores
Alternative app marketplaces like Amazon Appstore, Samsung Galaxy Store, and open-source repositories like F-Droid face new friction. If the Android OS treats all non-Play Store installations with extreme suspicion, users may be discouraged from exploring these alternatives due to the scary warning screens.
However, the existence of a bypass ensures that these stores can survive. It puts the onus on these third-party stores to educate their users. We may see a rise in “setup guides” provided by these stores, instructing users on how to configure their devices to accept external sources more seamlessly. This mirrors the desktop PC environment, where users must often approve “unsigned drivers” or applications from unidentified developers.
The Enterprise and MDM Perspective
For enterprise environments, these changes are a boon. Mobile Device Management (MDM) solutions can now leverage these native OS restrictions to ensure that company-issued Android Phones cannot sideload apps, effectively eliminating the “Shadow IT” problem on mobile. Conversely, for developers within a company who need to test internal builds, the power user bypass allows IT admins to push specific configuration profiles that whitelist internal signing keys, streamlining the testing process without compromising the entire fleet.
The Developer Experience
For Android developers, particularly those working on system utilities or experimental apps, the workflow becomes slightly more complex but ultimately more secure. Developers will need to be more transparent about why their apps require sensitive permissions. If an app triggers a “Restricted Setting” warning, the developer must explain to their user base why that permission is necessary and guide them through the bypass process. This transparency builds trust and filters out low-quality apps that request permissions they don’t need.
Pros, Cons, and Recommendations for Power Users
As we navigate this new terrain, it is crucial to weigh the benefits against the drawbacks and establish best practices for managing Android Gadgets in a restricted environment.
Pros of the New Security Model
- Reduced Malware Infection Rates: By adding friction to the installation of high-risk apps, the vast majority of accidental infections will be stopped.
- Protection Against Social Engineering: Scammers often guide victims through enabling settings over the phone. Complex bypass mechanisms make this significantly harder for attackers to orchestrate.
- Preservation of Choice: Unlike iOS, the option to sideload remains. The door is heavier to open, but it is not locked.
Cons and Potential Pitfalls
- User Friction: Legitimate apps from safe sources (like GitHub releases or Humble Bundles) may be flagged, causing confusion and frustration.
- Monopoly Concerns: Critics argue that making sideloading harder reinforces Google’s dominance over app distribution, potentially hurting competition.
- Complexity for Novices: Enthusiasts who are learning the ropes might find the new bypass steps intimidating, potentially stifling the next generation of tinkerers.
Best Practices for Safe Sideloading
If you intend to utilize the power user bypass to sideload applications on modern Android Phones, adhere to the following security hygiene practices:
- Verify Checksums: Always check the SHA-256 hash of the APK you are downloading against the developer’s official website. This ensures the file hasn’t been tampered with in transit.
- Use Virtual Machines or Sandboxes: For high-risk testing, consider using Android features like “Guest Mode” or specialized apps that create a virtual environment (like Island or Shelter) to isolate sideloaded apps from your main data.
- Audit Permissions Post-Installation: Even if you bypass the installation restriction, immediately go to the app’s settings and revoke any permissions that seem unnecessary for its core function.
- Stay Updated on Android News: Security protocols change with monthly security patches. What works as a bypass today might be patched or moved tomorrow. Keeping up with the community is essential.
Conclusion
The narrative surrounding Android Gadgets is evolving from one of unrestricted freedom to one of “responsible openness.” The introduction of stricter sideloading checks, balanced by a deliberate bypass for power users, represents a maturation of the platform. It acknowledges that while Android must be secure enough for banking and enterprise use, it must not lose the hacker spirit that made it popular in the first place.
For the average user, these changes will operate invisibly, providing a safer experience with fewer malware intrusions. For the power user, the capability to modify, tinker, and install any software remains intact—it simply requires a more intentional interaction with the device. This compromise ensures that Android remains the most versatile mobile operating system on the market, capable of serving both the security-conscious consumer and the tech-savvy enthusiast. As we look toward future Android updates, this delicate balance between security and sovereignty will likely continue to be the platform’s defining characteristic.