Your Android Phone’s Hidden Danger: A Deep Dive into Commercial Spyware
In an era where our lives are intricately woven into the digital fabric of our smartphones, Android phones have become more than just communication devices; they are personal vaults. They hold our private conversations, financial data, cherished memories, and professional secrets. This concentration of sensitive information makes them a prime target for a new and insidious class of threat: commercial-grade spyware. Unlike common malware, this sophisticated surveillance software is developed by for-profit companies and sold as a turnkey solution, enabling broad and intrusive monitoring of a target’s digital life. This article provides a comprehensive technical analysis of this growing threat, exploring how it operates, the vulnerabilities it exploits, and the crucial steps every Android user must take to fortify their digital defenses.
Understanding the Threat: The Anatomy of Commercial Android Spyware
The proliferation of powerful Android gadgets has unfortunately been paralleled by the rise of equally powerful malicious tools. To effectively defend against them, we must first understand their nature, their methods of infection, and their ultimate objectives. Commercial spyware represents a significant evolution from the adware or ransomware that users might be more familiar with.
What is Commercial Spyware?
Commercial spyware is a category of malicious software created and sold by private companies to third parties. These tools are designed for covert, persistent surveillance of a mobile device. The “commercial” aspect is key; this isn’t the work of lone hackers but of organized entities with development teams, sales departments, and customer support. Their products are often marketed under the guise of legitimate monitoring tools for parental control or employee tracking, but their capabilities far exceed these ethical boundaries. They grant the operator near-total control over the infected device, effectively turning a personal smartphone into a 24/7 surveillance device. This distinguishes them from state-sponsored cyberweapons, which are typically reserved for high-level espionage, by making advanced surveillance capabilities accessible to a much wider range of actors.
Common Infection Vectors
The developers of this spyware employ a variety of sophisticated techniques to deploy their payloads onto target Android phones. These methods are designed to be subtle and exploit both technological vulnerabilities and human psychology.
- Zero-Click Exploits: This is the most alarming vector. A device can be infected without any interaction from the user whatsoever. The spyware exploits vulnerabilities in the operating system’s code or in applications that handle data, such as messaging apps or email clients. A specially crafted message or data packet is all it takes to trigger the vulnerability and install the malware.
- One-Click Exploits: A more common method involves social engineering. The target receives a message—via SMS, WhatsApp, email, or social media—containing a link. This message is often carefully crafted to create a sense of urgency or curiosity, tricking the user into clicking. The link leads to a malicious website that exploits a browser vulnerability to install the spyware.
- Malicious Applications: The spyware can be hidden inside a seemingly legitimate application. While Google Play Protect is effective, these apps are often distributed through third-party app stores or sideloaded directly via an APK file. They might masquerade as a utility, a game, or even an antivirus program.
- Physical Access: In some scenarios, an attacker with just a few minutes of physical access to an unlocked device can manually install the spyware.
The Goal: Total Information Dominance
Once installed, the spyware’s objective is to achieve complete control and exfiltrate as much data as possible. Its capabilities are extensive and deeply invasive, including: vacuuming up emails, text messages, and chat logs from secure apps like Signal and Telegram; recording both incoming and outgoing phone calls; secretly activating the microphone to listen in on nearby conversations; accessing the camera to take photos and videos; and tracking the device’s precise GPS location in real-time. By logging keystrokes and capturing screenshots, it can steal passwords and other credentials, providing a complete, granular picture of the victim’s life.
Bypassing the Fort: How Spyware Infiltrates and Persists on Android

The Android operating system is built on a robust security model, featuring application sandboxing, a permission-based system, and numerous other protections. However, commercial spyware is engineered specifically to find and exploit the cracks in this fortress. Its success hinges on exploiting vulnerabilities, achieving deep system-level access, and operating with extreme stealth.
Exploiting Vulnerabilities for Privilege Escalation
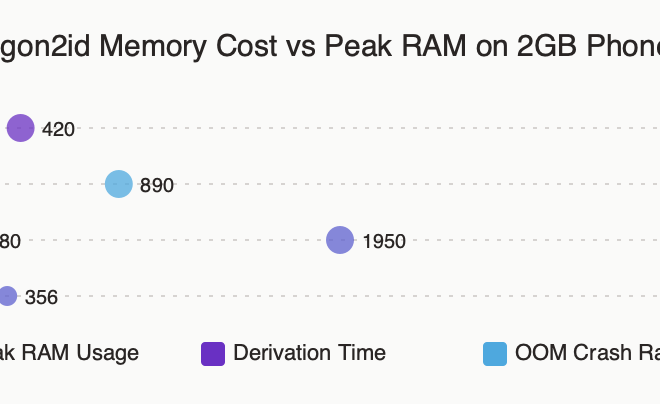
The initial infection is often just the first step. To gain the deep access it needs, spyware must elevate its privileges, effectively breaking out of the standard Android security sandbox. It achieves this by exploiting vulnerabilities (often tracked as Common Vulnerabilities and Exposures, or CVEs) in the Android OS, the Linux kernel it’s based on, or even hardware drivers. These exploits can allow the spyware to gain “root” access, which is the equivalent of having administrative control over the entire system. The fragmentation of the Android ecosystem plays a significant role here. While Google may release a patch, it can take weeks or months for some manufacturers to push that update to their specific models, leaving a wide window of opportunity for attackers to exploit known flaws on unpatched Android phones.
Achieving Persistence and Stealth
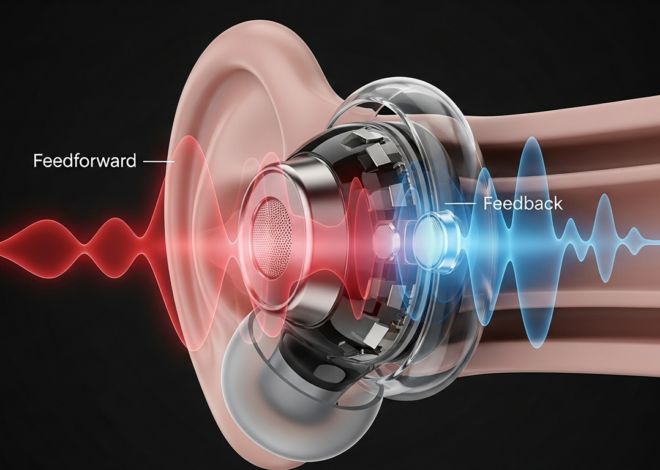
A key design goal for spyware is to remain on the device undetected for as long as possible. To do this, it employs a range of cloaking techniques. After gaining root access, it can embed itself in the system partition, making it resistant to a standard factory reset. It will often disguise its processes with innocuous names that mimic legitimate system services (e.g., “SystemUpdateService” or “SyncManager”). The application icon is typically hidden from the home screen and app drawer, leaving no visible trace of its presence. Furthermore, it meticulously manages its resource consumption, such as CPU and battery usage, to avoid creating the noticeable performance degradation that might alert a savvy user.
The Data Exfiltration Pipeline
Stealing the data is only half the battle; the spyware must then send it back to its operator without being detected. This process, known as exfiltration, is handled with care. The collected data—call logs, messages, GPS coordinates—is first stored in a hidden, encrypted file on the device. The spyware then establishes a covert communication channel to a command-and-control (C2) server. To avoid detection by network monitoring tools, this communication is always encrypted. The data is often broken up into small chunks and transmitted intermittently to blend in with normal network traffic. The spyware can even be configured to only upload data when the device is connected to a Wi-Fi network to avoid causing suspicious spikes in the user’s mobile data usage, which might otherwise be a red flag.
The Human Cost: Impact and Detection of Advanced Spyware
The technical sophistication of commercial spyware is matched only by the severity of its real-world impact. Its deployment can have devastating consequences for individuals’ privacy, safety, and security. Because it is designed for stealth, detecting it is exceptionally difficult, often requiring technical expertise and specialized tools.
Real-World Scenarios and Impact

The misuse of these powerful tools has profound implications. Consider these realistic scenarios:
- Corporate Espionage: A high-level executive’s phone is compromised before a major merger negotiation. The spyware activates the microphone during confidential board meetings, leaking strategic plans to a competitor and causing millions in financial losses.
- Targeting of Dissidents: A journalist working on a sensitive investigation is targeted. The spyware exfiltrates their communications with anonymous sources from encrypted messaging apps, putting those sources in grave danger and stifling freedom of the press.
- Domestic Abuse and Stalking: In a particularly sinister application, an abuser uses spyware to monitor their partner’s every move, conversation, and interaction. The GPS tracking, message interception, and ambient listening capabilities create an inescapable digital prison for the victim.
Subtle Signs of a Compromised Device
While top-tier spyware is nearly invisible, less sophisticated variants can sometimes leave subtle clues. It’s crucial to understand that these signs are not definitive proof of a compromise and can often be caused by buggy apps or aging hardware. However, a combination of these symptoms warrants investigation:
- Unexplained Battery Drain: The device’s battery depletes much faster than usual, even with light usage, as the spyware runs constantly in the background.
- Excessive Data Usage: A sudden, inexplicable spike in mobile or Wi-Fi data consumption could be the spyware uploading collected information.
- Overheating: The phone feels warm to the touch even when it’s idle, a result of the processor being constantly engaged by the malicious process.
- Anomalous Behavior: The screen lights up randomly, the device reboots on its own, or it takes an unusually long time to shut down. You might also receive strange, garbled text messages which can sometimes be command codes from a C2 server.
Staying informed through reliable Android News sources about emerging threats is a key part of recognizing potential signs of compromise.
Building Your Defenses: Practical Steps to Secure Your Android Phone
While the threat of commercial spyware is serious, users are not powerless. A security-conscious mindset combined with proactive hygiene can dramatically reduce the risk of infection. The goal is to make your device a hardened, difficult target.

Proactive Security Measures
These are the foundational best practices that every user of Android Phones should adopt:
- Update Immediately and Consistently: This is the single most important defense. Install system and security updates from your device manufacturer and app updates from the Google Play Store as soon as they are available. These patches fix the very vulnerabilities that spyware exploits.
- Scrutinize Your Apps: Only install applications from the official Google Play Store. Avoid sideloading APKs from untrusted websites. Before installing any app, review its requested permissions. Does a simple calculator app really need access to your contacts and microphone? If a permission request seems excessive, deny it or don’t install the app.
- Lock Down Your Lock Screen: Protect your device from unauthorized physical access. Use a strong, complex password or PIN instead of a simple pattern or basic facial recognition.
- Practice Phishing Awareness: Be inherently skeptical of unsolicited links or attachments received via email, SMS, or messaging apps, even if they appear to come from a known contact whose account may have been compromised.
Advanced Hardening Tips
For users who are at higher risk or simply want to enhance their security posture:
- Reboot Regularly: A simple daily reboot can sometimes disrupt and remove less-persistent forms of malware or spyware that haven’t embedded themselves deep into the system.
- Use Lockdown Mode: Familiarize yourself with your phone’s Lockdown Mode. When enabled, it temporarily disables biometric unlocking (fingerprint, face) and hides notification content on the lock screen, forcing a PIN or password. This is useful if you feel you might be forced to unlock your device.
- Perform Security Audits: Periodically review the list of installed apps on your device and uninstall anything you don’t recognize or no longer use. Check which apps have been granted sensitive permissions, such as location, microphone, or accessibility services access.
Conclusion
The rise of powerful, commercially available spyware represents a formidable challenge to the privacy and security of every Android user. These tools transform the incredible Android gadgets we rely on into potential instruments of surveillance, capable of capturing the most intimate details of our lives. However, understanding the threat is the first step toward mitigating it. By recognizing the infection vectors, appreciating the technical sophistication of these tools, and—most importantly—adopting a rigorous and consistent security hygiene, users can build a strong defense. The ongoing battle between security researchers and spyware developers means that vigilance is not a one-time task but a continuous commitment. Keeping your device updated, being cautious about what you install, and staying informed are the cornerstones of protecting your digital life in an increasingly complex threat landscape.